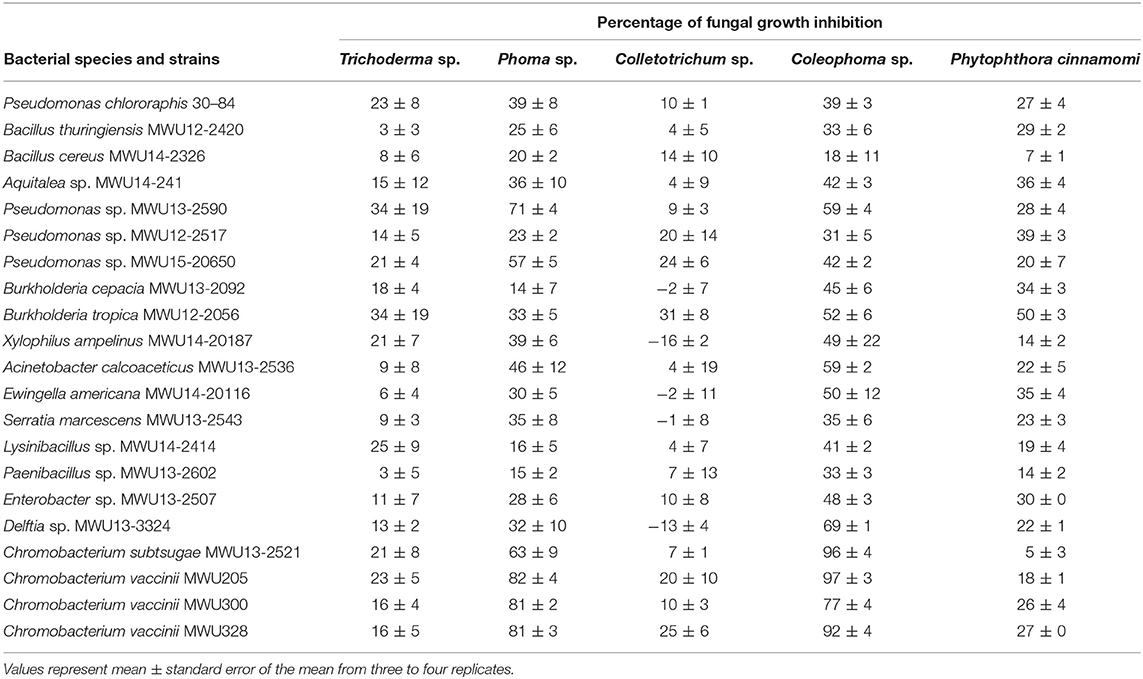
Frontiers | Inhibition of Fungal Growth and Induction of a Novel Volatilome in Response to Chromobacterium vaccinii Volatile Organic Compounds | Microbiology

Expression and subcellular localization of kinetoplast-associated proteins in the different developmental stages of Trypanosoma cruzi | SpringerLink

Tracheal epithelial cells respond to bitter tastants and artificial... | Download Scientific Diagram
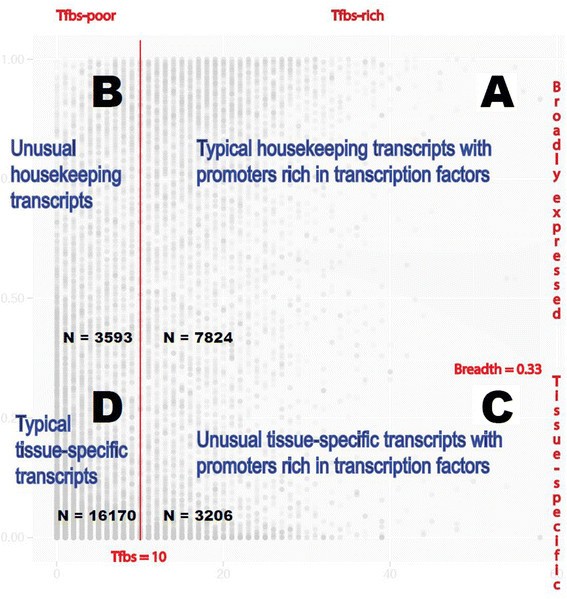
A simple metric of promoter architecture robustly predicts expression breadth of human genes suggesting that most transcription factors are positive regulators | Genome Biology | Full Text

Adaptor FYB (Fyn-binding protein) regulates integrin-mediated adhesion and mediator release: Differential involvement of the FYB SH3 domain | PNAS